Net phishing
In this post I’m going to discuss about net phishing (also referred to as “web spoofing”). I still hear about people that have lost real money because of net phishing – and that´s just sad.
Net phishing isn’t a new technique and neither a qualified hacking technique, but then keep in mind that most hacks today is based on old hacks, just new vulnerabilities.
What Is Net Phishing?
This is how it’s defined on wikipedia
Phishing is the attempt to acquire sensitive information such as usernames, passwords, and credit card details (and sometimes, indirectly, money) by masquerading as a trustworthy entity in an electronic communication.
This method has been used since ages and is still filling most of our mailboxes with scam mail from banks, lottery and viagra offers. When performing a net phishing attack, the goal is to throw a bate to as many people as possible and make them arrive to an authority site (such as a bank or e.g. Facebook) which is identical or similar to the original.
The victim is then asked for credentials. This credentials can then be used to take over a account and e.g. transfer money to a foreign country.
How It’s Done
- E-mail list is obtained. Most likely bought on “black market” or extracted from leaked database dumps
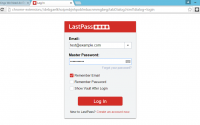
- Authority website is selected and cloned (downloaded and then uploaded)
e.g. using: https://www.httrack.com or wget - Many times the criminal buys a domain with similar domain name (such as bank2015 or bank.io)
- The URL to the new, cloned site is sent out to thousand, possible hundred thousands of potential victims
- When victim arrives to the cloned sites, he is tricked to reveal sensitive information
- Money is withdraw from the victims account in a foreign country
Tricks They Use
Over the years I have seen that they use many tricks. Here’s a few to watch up for.
Authority
They put a name and a address on the E-mail which gives it more authority
Bypassing spam filters
They mix the words around so the exact same mail does’t go to all the users
Russian girl
Sometimes they send a “friendly” mail. It usually includes an image of a good looking Russian girl. When that image is loaded from their web server they know that the mail address is in use. An active mail address is more valuable then one that will increase the spam score (increase the odds for ending up in junk folder)
Skipping website
Sometimes they skip website entirely and either trying to initiate contact with victim or asking directly for confidential information
Recommended reading: Social Engineering: Phishing latest and future techniques
How You Can Protect Yourself
- Always check on which URL (If not even URL: Warning!) you end up to
- Two part authentication makes it hard
- Check the language
- All big sites has SSL
- Never ever reply with confidential information
… and as my old dad use to say:
If something is to good to be true, it’s probable not.
References (and tips for reading)
Learning to Detect Phishing Emails
http://www.ra.ethz.ch/CDStore/www2007/www2007.org/papers/paper550.pdf
What are phishing scams
https://www.comodo.com/resources/home/what-are-phishing-scams.php